You probably know that you can encrypt and sign your emails using GnuPG, and there's even a bunch of programs and plugins to make it easier for you. However, if you are like me and use Gmail's browser interface, there's no plugin for you. Your only choice is to copy & paste your mails to some external program, encrypt / decrypt them and paste them back into Gmail. Certainly not very comfortable.
Today, I set out to change this. I wrote a small Chrome extension which interfaces with GnuPG so you can encrypt and decrypt your mails directly from the browser. It uses a very simple mechanism - pipes. Using the excellent [cached]"stx-execpipe" library, I wrote a small NPAPI plugin that handles all calls to GnuPG.
With all error checking removed, it boils down to a few lines of code:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 | |
The special --use-agent option ensures gpg will pop up a window to ask the user for his password when it's needed - it will stay as far away from the browser as possible!
That's basically the design for the whole plugin, it's just variations on the arguments for decryption, signing, etc. The NPAPI interface is handled by [cached]FireBreath, a most excellent framework you should definitely check out if you want to write your own plugin.
Communication with the browser is handled by a Chrome extension. It provides entries in the context menu when the user selects text, so he can directly encrypt the selection. The output of gpg will then be pasted into the clipboard.
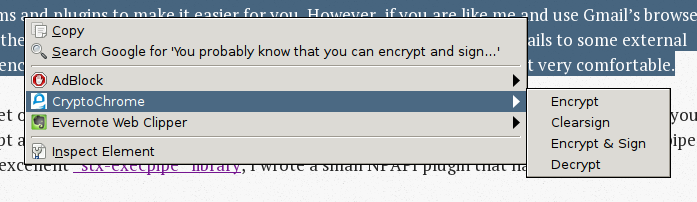
For future version, in-place encryption and decryption is planned, but it's not yet implemented yet. For now, select, right-click to encrypt and then paste is all you need. Also note that all needed keys have to be present in your gpg keychain - right now, the plugin won't query external servers for them.
If you have any ideas on how to improve this (I sure as hell have), please let me know. Of course, the source is on GitHub: [cached]CryptoChrome
Tags: security, privacy, programming